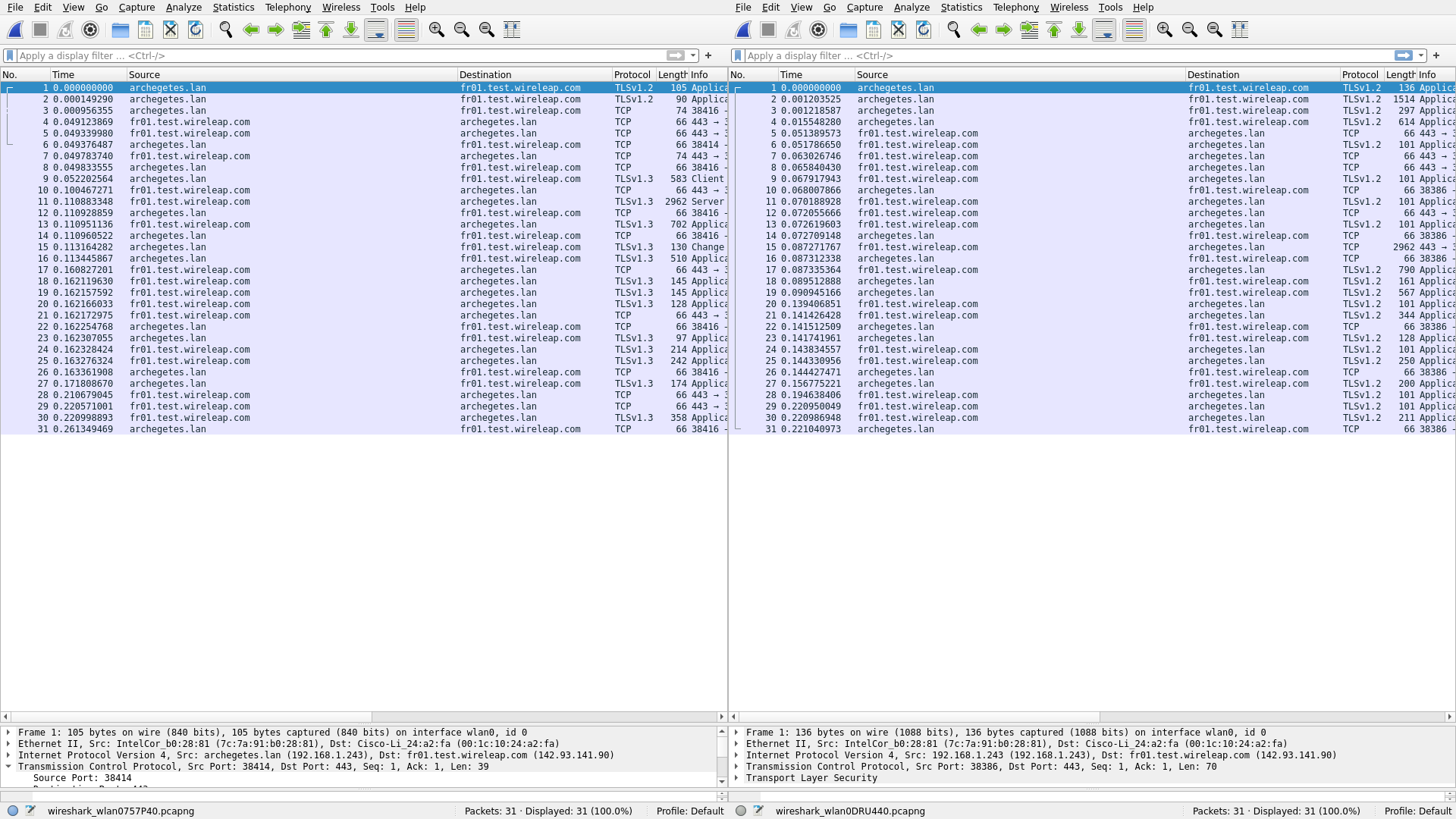
Side by side traffic comparison
The following image is a side-by-side comparison of two browsing
sessions captured with Wireshark. One is browsing to
fr01.test.wireleap.com, while the other is using the wireleap client
(configured with 2 hops, the first hop being fr01.test.wireleap.com)
to browse elsewhere.
Can you tell which is which?
Show answer
Answer: The wireleap connection is on the right.
On the left (raw connection) you can see wireshark dissecting the TLS handshake but not on the right (since it already happened once when establishing a connection to fr01 before) so it’s all just “application data”.
So, there are subtle differences because of the different TLS session length/establishment but as you can see it’s pretty close on a packet by packet basis. Regarding the TLS version differences, TLS 1.3 is being forced in the code, the assumption is nginx lazily keeping the fronting connection to 1.2, and Firefox negotiating an upgrade to 1.3 on the left. But, wireleap didn’t – which is something to look into.
The results are very raw, testing conditions not ideal, and we have yet to put effort into this aspect of Wireleap, but none the less for a naive starting point it’s pretty interesting.
Tags
Previous Article
Inline client upgrades, UI fixes and improvements